Mastering AWS Security - Post 4: Amazon Inspector - Continuous Vulnerability Scanning
Hey there! I’m a seasoned Solution Architect with a strong track record of designing and implementing enterprise-grade solutions. I’m passionate about leveraging technology to solve complex business challenges, guiding organizations through digital transformations, and optimizing cloud and enterprise architectures. My journey has been driven by a deep curiosity for emerging technologies and a commitment to continuous learning.
On this space, I share insights on cloud computing, enterprise technologies, and modern software architecture. Whether it's deep dives into cloud-native solutions, best practices for scalable systems, or lessons from real-world implementations, my goal is to make complex topics approachable and actionable. I believe in fostering a culture of knowledge-sharing and collaboration to help professionals navigate the evolving tech landscape.
Beyond work, I love exploring new frameworks, experimenting with side projects, and engaging with the tech community. Writing is my way of giving back—breaking down intricate concepts, sharing practical solutions, and sparking meaningful discussions. Let’s connect, exchange ideas, and keep pushing the boundaries of innovation together!
1. Introduction to Amazon Inspector
What is Amazon Inspector?
Amazon Inspector is an automated vulnerability management service that continuously scans your AWS workloads for known software vulnerabilities and unintended network exposure. It helps improve the security posture of applications deployed on Amazon EC2, AWS Lambda, and container images stored in Amazon ECR.
Legacy vs. Modern Inspector
Amazon Inspector was originally launched as an on-demand security assessment tool. The newer version (Inspector v2) is agentless for most resources, continuous in nature, and deeply integrated with other AWS services for automation and scale.
Why It Matters
Cloud-native apps face evolving threats. Inspector provides scalable, near real-time visibility into vulnerabilities, helping meet compliance needs and reduce the attack surface.
Supported Resource Types
EC2 Instances
Lambda Functions
Amazon ECR Container Images
2. Core Concepts & Architecture
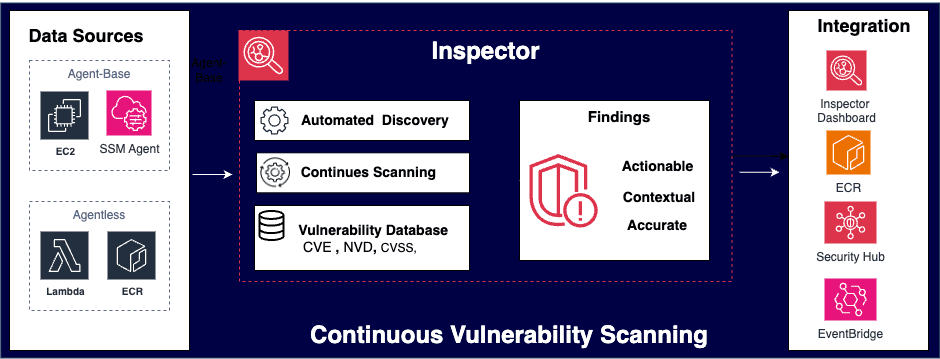
How Inspector Works

Once enabled, Inspector automatically discovers resources, evaluates them against known CVEs (Common Vulnerabilities and Exposures), calculates exploitability and severity scores using CVSS, and generates findings.
The findings are then aggregated in the Inspector console, pushed to AWS Security Hub and Amazon EventBridge, and also sent to ECR for container images.
It support Agent-Based and Agentless Scanning
Amazon Inspector leverages:
AWS Systems Manager (SSM) agent for EC2 instance scans (Agent-Based)
AWS Lambda layer introspection (Agentless)
ECR API event triggers for container scans (Agentless)
Vulnerability Data Sources
CVE (Common Vulnerabilities and Exposures)
NVD (National Vulnerability Database)
Vendor-specific advisories
Key Components
Scan Types: Continuous and event-driven
Finding Types: Software vulnerabilities (CVE), network reachability, permissions misconfigurations
Severity Levels: Critical, High, Medium, Low, Informational
Delegated Admin: Central management across AWS accounts
3. Supported Workloads & Scan Types
EC2: Uses SSM agent to inspect installed packages and configurations
Lambda: Scans function code for vulnerabilities
ECR Containers: Event-driven scans when images are pushed or pulled
Scan Frequency: Continuous for supported resources; can also be initiated manually
4. Amazon Inspector Findings
Finding Metadata
Resource ID, Region, CVE ID, Affected Package
Exploitability score, CVSS Base Score, Description
Lifecycle
Active: Unresolved vulnerability
Closed: Resolved due to patching or resource removal
Suppressed: Manually ignored via suppression rules
Suppression Rules
Helps reduce noise and focus on actionable issues
Example Finding:
{
"findingArn": "arn:aws:inspector2:us-east-1:123456789012:finding/123abc456def",
"resourceId": "i-0abc123456def7890",
"resourceType": "Ec2Instance",
"region": "us-east-1",
"packageVulnerabilityDetails": {
"vulnerabilityId": "CVE-2023-25610",
"source": "NVD",
"affectedPackages": [
{
"name": "openssl",
"version": "1.1.1k-1.el8",
"epoch": "1",
"release": "1.el8",
"architecture": "x86_64"
}
],
"cvss": [
{
"baseScore": 9.8,
"vector": "CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H",
"source": "NVD",
"version": "3.1"
}
],
"relatedVulnerabilities": ["CVE-2023-25610"],
"exploitabilityScore": 3.9,
"description": "The openssl package is vulnerable to a buffer overflow which may allow remote attackers to execute arbitrary code via crafted input. Affected version is 1.1.1k-1.el8."
},
"severity": "CRITICAL",
"firstObservedAt": "2024-12-01T12:34:56Z",
"lastObservedAt": "2025-05-10T09:45:21Z",
"status": "ACTIVE"
}
5. Setting Up Amazon Inspector
Enabling the Service
Via AWS Console: Amazon Inspector > Activate Inspector
Via CLI:
aws inspector2 enable
IAM Requirements
Inspector requires specific permissions and SSM agent installed on EC2
Use of IAM roles for Lambda scanning and cross-account configurations
| Component | IAM Role / Policy Needed | Setup Required? |
| EC2 Scanning (SSM Agent) | AmazonSSMManagedInstanceCore for EC2 Instance | ✅ Yes (manual) |
| Inspector Core | AWSServiceRoleForAmazonInspector2 (auto-created) | ❌ No (auto unless blocked) |
| Lambda Scanning | No extra roles needed (uses Inspector role) | ❌ No |
| Cross-Account Setup | Trust & delegation via Organizations | ✅ Yes (manual) |
AWS Organizations
Auto-enable across Org with Delegated Admin
Consolidated findings for centralized security operations
6. Deep Dive: Container Image Scanning (ECR)
How It Works
Inspector listens for ECR image push/pull events
Scans image layers and dependencies
Associates CVEs with the image metadata
Best Practices
Use immutable tags
Regularly rebuild images with latest patches
Integrate scan reports into CI/CD pipelines
7. Integration with Other AWS Services
Security Hub: Findings ingested and normalized
EventBridge: Triggers remediation workflows
SNS: Send email/SMS alerts on critical findings
GuardDuty vs. Inspector:
GuardDuty: Threat detection (runtime, network behavior)
Inspector: Vulnerability detection (static, package-level)
SSM Patch Manager: Automated remediation of EC2 findings
8. Automating with Amazon Inspector
EventBridge + Lambda Example:
When Inspector finds a CRITICAL vulnerability, invoke Lambda to tag the EC2 instance as “VULNERABLE”.
aws events put-rule \
--name InspectorCriticalFinding \
--event-pattern '{
"source": ["aws.inspector2"],
"detail-type": ["Inspector2 Finding"],
"detail": {
"severity": ["CRITICAL"]
}
}' \
--state ENABLED
Lambda function can tag, isolate, or remediate based on severity.
Enable Amazon Inspector across Org Accounts
enable Org account
# Enable Inspector service access for the organization
aws organizations enable-aws-service-access \
--service-principal inspector2.amazonaws.com
# Register delegated admin (must be run from Org master account)
aws inspector2 enable-delegated-admin-account \
--delegated-admin-account-id $ORG_ADMIN_ACCOUNT_ID \
--region $REGION
### === STEP 2: Log into Delegated Admin Account and Enable Inspector Org-Wide === ###
# Enable Inspector for delegated admin account
aws inspector2 enable \
--account-ids $ORG_ADMIN_ACCOUNT_ID \
--resource-types EC2,ECR,Lambda \
--region $REGION
# Enable auto-enable for new accounts
aws inspector2 update-organization-configuration \
--auto-enable "ec2=true,ecr=true,lambda=true" \
--region $REGION
### === STEP 3: Enable Inspector for Existing Static Member Accounts === ###
aws inspector2 enable \
--account-ids $EXISTING_MEMBER_ACCOUNTS \
--resource-types EC2,ECR,Lambda \
--region $REGION
9. Monitoring and Reporting
Inspector Dashboard: Real-time visibility into findings
CloudWatch Metrics:
Number of active findings
Severity distribution
Reporting:
Export findings to CSV
Schedule periodic summaries via Lambda
10. Security and Compliance Use Cases
CIS Benchmarks: Supplement Inspector with AWS Config rules
PCI-DSS, HIPAA, ISO 27001: Inspector findings map to controls
Continuous Compliance: Use EventBridge + Lambda to monitor drift
11. Architect-Level Insights
Multi-Account Strategy:
Use Delegated Admin
Aggregate findings in Security Hub
Integration in Landing Zones:
Use SCPs to enforce Inspector enablement
Use Control Tower lifecycle events
DevSecOps Pipelines:
Trigger Inspector container scans on CI/CD image builds
Fail builds based on CVSS threshold
Cost Optimization:
Disable scans in non-prod accounts
Use tag-based exclusions for ephemeral resources
12. Exam Tips - Key Concepts to Remember
| Concept | What to Know |
| Inspector v2 | Latest version (Inspector v2) is agentless for ECR and Lambda, but EC2 scanning still requires the SSM agent. |
| Findings Scope | Inspector scans for software vulnerabilities (CVEs), network reachability, and Lambda package risks. |
| Findings Destination | Findings are automatically sent to Amazon EventBridge; you must set up custom rules to forward them to SNS, Lambda, or Security Hub. |
| IAM | Inspector uses a service-linked role (AWSServiceRoleForAmazonInspector2). EC2 needs the AmazonSSMManagedInstanceCore policy. |
| Cross-Account | Requires delegated administrator setup with AWS Organizations. You must register member accounts explicitly. |
| Auto Remediation | Can be achieved via EventBridge + Lambda to auto-patch, tag, isolate, or notify. |
| ECR Scanning | Inspector scans containers automatically on image push or periodically for supported base images. |
| Lambda Scanning | Inspector detects vulnerable libraries in Lambda function code and layers—no agent needed. |
Conclusion
Amazon Inspector is a critical part of a modern, automated cloud security strategy. Whether you're a beginner learning the basics or a specialist architecting enterprise-grade security, mastering Inspector empowers you to reduce risk, maintain compliance, and integrate security into every layer of your cloud infrastructure.
This article is Part 4 of the blog series “Mastering AWS Security Specialty” If you missed previous posts please check below.
👉 Part 1: Deep Dive into IAM – Core of AWS Security
👉 Post 2: CloudTrail – Your First Line of Forensics